No products in the cart.

The Hidden Dangers of Microsoft’s Task Scheduler by Gilbert Oviedo Most Windows users run their computers on a daily basis and while they may take steps to protect themselves, hidden dangers lurk in the form of the “Task Scheduler”. The task scheduler is a Microsoft program that mostly automates tasks....
Author
Latest Articles
 BlogJanuary 26, 2018Effects of Biometrics Co-Used with Password
BlogJanuary 26, 2018Effects of Biometrics Co-Used with Password BlogDecember 28, 2017Networks, What do you mean by that?
BlogDecember 28, 2017Networks, What do you mean by that?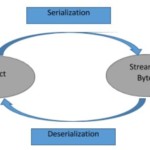 BlogDecember 4, 2017Thick Client Penetration Testing – Exploiting JAVA Deserialization Vulnerability for Remote Code Execution
BlogDecember 4, 2017Thick Client Penetration Testing – Exploiting JAVA Deserialization Vulnerability for Remote Code Execution BlogNovember 28, 2017Extending attack surface in distributed environments
BlogNovember 28, 2017Extending attack surface in distributed environments
Subscribe
Login
0 Comments
