| File | |
|---|---|
| PenTest_07_2013_teaser.pdf |
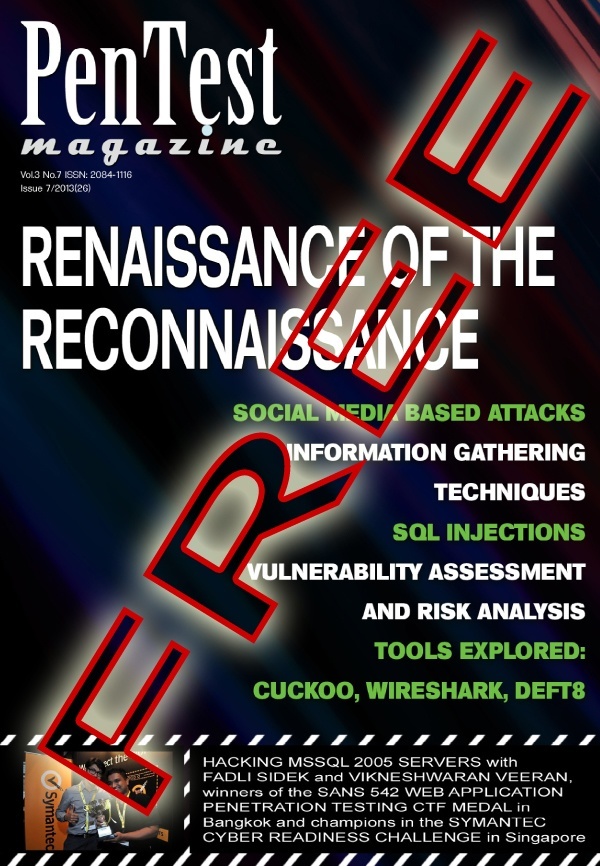
Dear PenTest Readers,
We would like to present you the TEASER of the upcoming PenTest Regular ‘Renaissance of the Reconnaissance’. In the full issue you will be able to read about:
- Vulnerability Management and Risk Analysis;
- Tools: DEFT8, Wireshark, and Cuckoo;
- Techniques: Information Gathering Techniques, Social Media Attacks, Code Injections.
- Hunting and hacking MSSQL 2005 servers by multiple CTF events winners.
LET’S TALK ABOUT SECURITY
Vulnerability Assessment and Management: Integrated Approach
By Muhammad Saleem
Vulnerability Assessment and Management is the core component of any security program. In modern approach, to handle latest security challenges and zero day attacks, we have to think like hackers think, our approach to handle vulnerabilities should be based on hackers’ look into vulnerabilities.
Risk Analysis: Why it is so Critical for HIPAA Compliance
By Swati Sharma
Breach investigations on Hospice of North Idaho (HONI) and AHMC Healthcare have made crystal clear how much critical it is to understand the risk associated with the electronic protected health information (ePHI). The spokesperson of HHS has made the statement on the HONI case: ‘HONI did not conduct an accurate and thorough risk analysis to the confidentiality of ePHI as part of its security management process from 2005 through Jan. 17, 2012’.
TOOLS
A Tool-belt in your Pocket with DEFT8
By Curtis Purdy
There are rather cloudy lines between many of the fields of information security. Of all the tools we use here at sysec.info, none can be pigeonholed into only one of those three slots. Whether it is using EnCase for incident response to triage a breach, or BackTrack/Kali for forensics to quickly boot Wireshark and start sniffing and recording packets on a promiscuous interface, almost all tools in these three disciplines are multi-functional.
Wireshark in Penetration Testing
By Praveen Darshanam
Sniffers can be used by penetration testers during the information gathering. Its goal is to disclose crucial information about the network which we are going to penetrate. Sniffing is defined as passive way of information gathering since we never interact with any machine directly.
Extending Cuckoo Framework
By Christopher Ashby
In the previously published ‘Automating Malware Analysis with Cuckoo’, it was demonstrated how to install the Cuckoo sandbox malware analysis system and basic usage. In short, this framework allows for automated analysis of malicious specimens within a controlled environment. In this article we will describe some of the advanced features, extending the platform’s capabilities, and demonstrate how to tie all this analysis into a single report.
TECHNIQUES
Information Gathering Techniques
By Steven Wierckx
The very first step in both hacking attempts and penetration testing is called ‘information gathering’. It is often said that this step is (largely) invisible and undetectable. In this article I will discuss some information gathering techniques and I will point out how visible they are.
Launching Social Media Based Attacks
By Joseph Muniz
Social media is everywhere and can be used as a method to breach your network. Together with my colleague, Aamir Lakhani, we tested this concept by completely compromising a company during an authorized penetration test.
From SQL Injection to 0wnage Using SQLMap
By Shrikant Gangadhar Antre
An SQL injection attack consists of insertion or ‘injection’ of an SQL query via an input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data, execute administration operations on the database, recover the content of a given file present on the DBMS file system, and, in some cases, issue commands to the operating system.
The Other Side of the Fence: How to Protect against Code Injection Attacks
By Azzedine Benameur, Nathan Evans, and Matthew Elder
Usually testing begins with a reconnaissance phase in which the penetration tester scans the network or a given machine, then identifies a target host and program, and tries to exploit a vulnerability. The best result for a penetration tester – and the worst for the organization under evaluation – is to allow remote code execution on a computer. In this article we present the other side of penetration testing: the defenses in place to protect a computer against remote code execution.
PLUS
Hunting and Hacking MSSQL 2005 Servers
By Fadli B. Sidek and Vikneshwaran Veeran
The objective of this article is to demonstrate how black box penetration testing on MSSQL servers can be performed and to illustrate a step-by-step approach from finding SQL services/ports to owning the whole box. The article takes a step further by also highlighting some suggestions for mitigation and prevention of such attacks.
| File | |
|---|---|
| PenTest_07_2013_teaser.pdf |

Post Comment