Description
| File | |
|---|---|
| preview w33 workshop issue.pdf |
In this e-book you will find text materials presented in the course “Effectively measuring and communicating pentest results. A CISO perspective.” During this course you will learn the major aspects of the penetration testing process that provides the most value to a security technician’s organization to improve its overall security posture. Much more goes on behind the scenes after the pentest report is delivered to various elements of the information security team, including the CISO. It’s important that the pentest is conducted and formatted in a manner in which senior leadership can make business decisions as a result of the pentest.
Already got a subscription? Click Here
Want to download free preview? Click Here
You will learn:
• Steps, tips and different ways of how to describe your work in an efficient way,
• How to create good presentation: what should it contain and what to avoid,
• How the PenTest results will be used to reduce risk to the organization,
• How to convert Technical Speak into Business Talk.
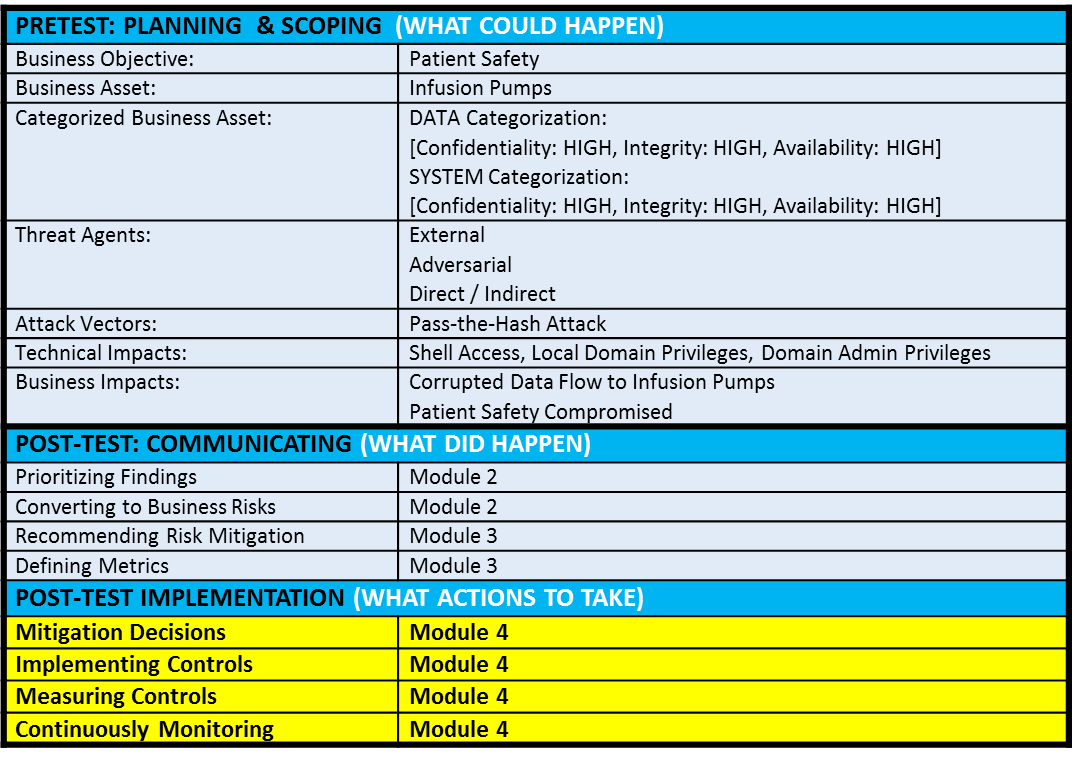
Here is the table presenting content that you will learn from this ebook:
Note: Some of the materials, like videos or particular exercise, are not presented in this issue. If you would like to gain access to all the materials, you have to buy a course.
The main aim of this e-book is to present our publication to a wider range of readers. We want to share the material we worked on and we hope we can meet your expectations. With free account you have access to all the teasers and open issues, but we fully believe that you’d like to take this one step further and enjoy our publications without limits. Our premium subscription contains access to our whole archive.
Enjoy your reading,
PenTest Magazine’s
Editorial Team
Only logged in customers who have purchased this product may leave a review.





Reviews
There are no reviews yet.