by Damon Mohammedbeger
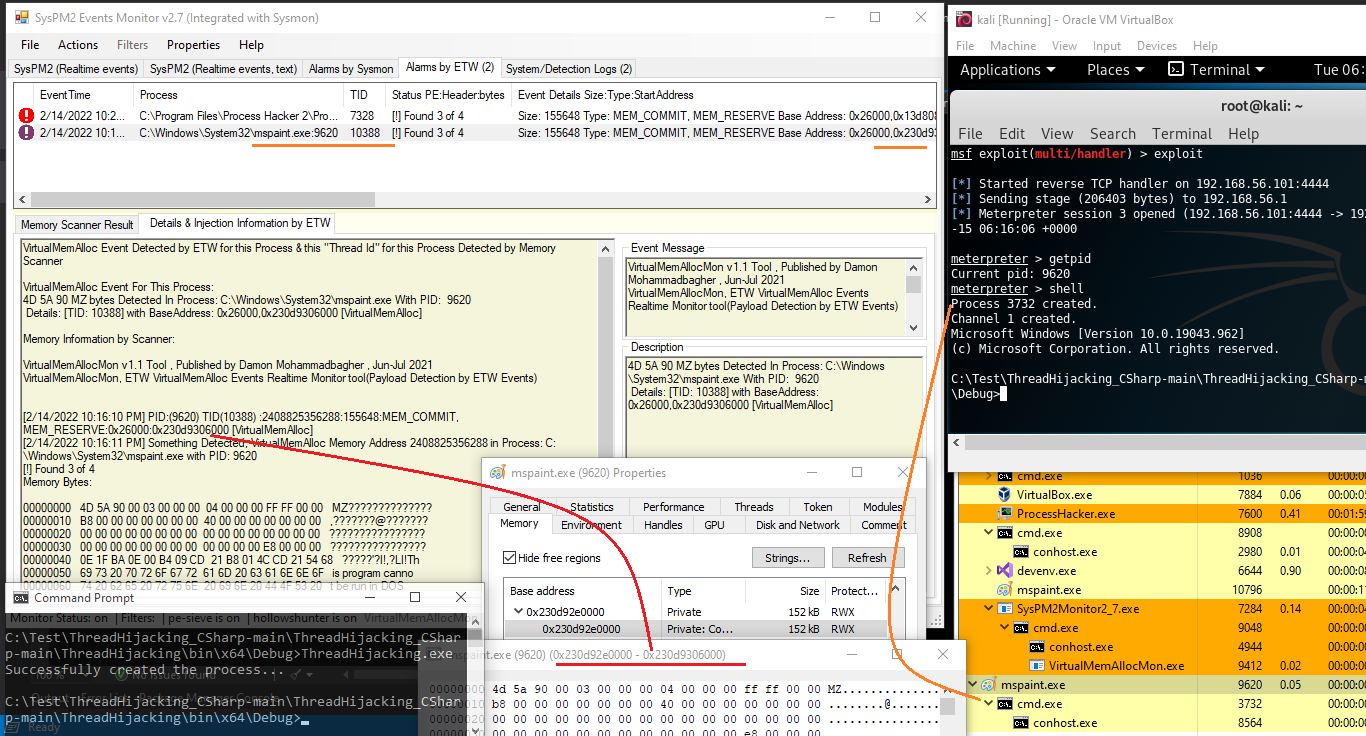
In this article, I want to talk about my research about ETW and Sysmon and how I can use these events for detection against C2 servers like Cobalt Strike, PoshC2, Sliver and, as always, Metasploit.
So, as a pentester and security researcher, I tried to work on the Blue-Team side (defensive approach) with my own offensive experience, etc.
In this article, I will talk about these things (which was some of my researches from two years ago about detection with a Blue-Teaming approach):
- My own tools created with C# for monitoring ETW/Sysmon Events (Real-time) and how can Detect Remote-Thread-Injection Attack via ETW/Sysmon Events to Detect Malware/backdoor or C2 Client Process also Detecting their Traffic!
- ETW vs Sysmon against Cobalt Strike
- ETW vs Sysmon against PoshC2
- ETW vs Sysmon against Sliver
- ETW vs Sysmon against Metasploit & talk about some bugs or problems I saw in my tools when as defender you want to use ETW or Sysmon.
- Using ETW VirtualMemAlloc Events for Detection
- PE MZ bytes Detection via Memory Scanner tool which made by C# and this memory scanner works based on ETW VirtualMemAlloc events.
Before I begin, I want to talk about 2017, because since 2016/2017 I started to work....
Author
Latest Articles
 OfficialFebruary 22, 2023Windows Privilege Escalation: The Concepts of Hijacking Execution Flow
OfficialFebruary 22, 2023Windows Privilege Escalation: The Concepts of Hijacking Execution Flow OfficialFebruary 22, 2023Building Intuition into Monitoring for OT/ICS Security
OfficialFebruary 22, 2023Building Intuition into Monitoring for OT/ICS Security OfficialFebruary 22, 2023WiFi Pentesting with Airodump-ng
OfficialFebruary 22, 2023WiFi Pentesting with Airodump-ng OfficialFebruary 21, 2023ETW vs Sysmon Against C2 Servers
OfficialFebruary 21, 2023ETW vs Sysmon Against C2 Servers
This article gives great insights into using ETW and Sysmon for detecting C2 servers. Papa’s pizzeria
This article on ETW vs Sysmon for detecting C2 servers is incredibly insightful for both security professionals and researchers. It’s great to see the offensive and defensive sides come together. Kind of like Retro Bowl — strategy and execution make all the difference!
I will learn this knowledge gradually
Just snagged my presentation from this service, and it’s a total win! No more last-minute stress or slides struggle. Buy presentation – https://studyfy.com/service/buy-presentation The design is on point, and the content? Epic. If you’re done with the presentation chaos, this is your go-to. Seriously, check it out – smooth presentations for the win!
I encourage you to participate in poppy playtime whenever you get the chance. This is a wonderful activity for relieving tension and unwinding after a long day.